SystemMen - This article will guide you how to convert SSL Nginx cert to Tomcat cert.
Nginx cert and Tomcat cert
When you buy SSL cert for Nginx web server (or Apache), you usually get 3 files of the following type:
- STAR_domain.CERT.crt
- STAR_domain.PRIVATE.key
- STAR_domain.CA.key
Nginx’s ssl cert file uses X.509 format. You can read more about it.
For Java applications, it runs the Tomcat web server. And Tomcat’s ssl cert uses the .jks (Java KeyStore) format, this is Oracle’s own format.
Recommended Reading: How to convert SSL Nginx cert to IIS cert
Steps to convert X.509 cert into JKS
First, this is easier on a Linux machine, because it has OpenSSL built-in.
To convert X.509 SSL cert to JKS cert, you need 3 files that I mentioned above, CERT file, PRIVATE key and CA cert.
Recommended Reading: Nginx redirect a location to another domain
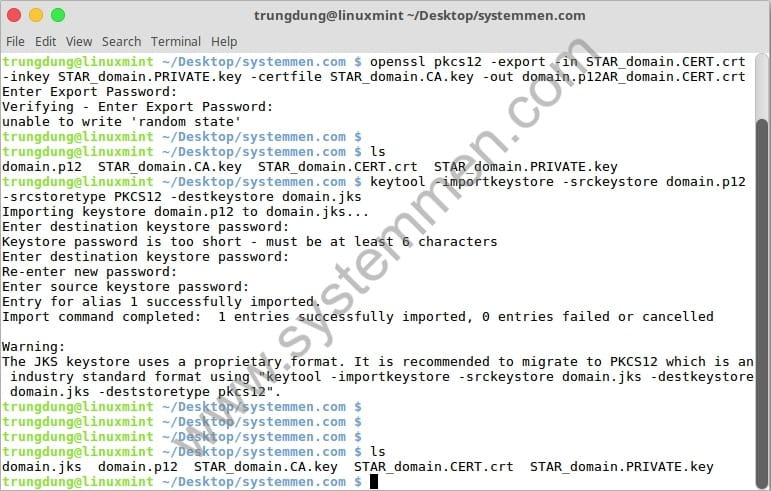
First, you need to export all of these files into one bundle file in .p12 format.
$ openssl pkcs12 -export -in STAR_domain.CERT.crt -inkey STAR_domain.PRIVATE.key -certfile STAR_domain.CA.key -out domain.p12
This command will ask you to set an export password for the keystore. For example, I set it to danie.
Then, run the keytool command to import this .p12 file into the PKCS12 library and export the final cert file .jks.
$ keytool -importkeystore -srckeystore domain.p12 -srcstoretype PKCS12 -destkeystore domain.jks
This command will ask you to set a destination keystore password, at least 6 characters. I set it to daniepham.
Then it will ask you to type source keystore password. It is the same password export that you have set at the openssl pkcs12 command, it’s danie of my example.
And done, you have finished converting X.509 cert to JKS cert and now you can import it into your Tomcat web server.
Conclusion
Converting X.509 cert of Nginx (or Apache) to Tomcat’s cert JKS only goes through 2 commands. It is not difficult, but not everyone knows that. Hope the article is useful for you.
«« How to install latest Nginx in CentOS 7How to convert SSL Nginx cert to IIS cert »»